When we talk about cybersecurity, we usually default to technical metaphors: firewalls, encryption, zero-day exploits. But more and more, it’s not code that’s being hacked, it’s cognition.
Welcome to the age of cognitive security, where the battlefield is the human mind.
This shift demands new thinking, and more importantly, new thinkers. That’s why I’ll be hosting and moderating a new virtual panel series called Cognitive Security Leadership Perspectives, brought to you by Maro,. The first webinar is Cognitive Security 101: Protection for the Human Attack Surface, on June 25th. We’re bringing together the sharpest minds in behavioral science, cybersecurity, gamification, and human-centered design to explore this important conversation and guide security and technology leaders Our goal: convene a multidisciplinary brain trust to tackle one of the most urgent and under-addressed issues in security today.
The Real Target: People, Not Just Systems
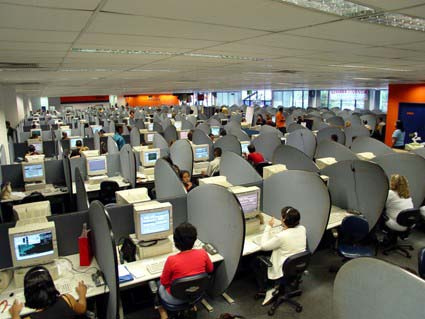
For years, organizations have poured billions into digital defenses, from endpoint detection to threat hunting. And yet, the majority of successful cyberattacks still exploit human vulnerabilities. According to the 2025 Data Breach Investigations Report, , 60% of breaches involve the human element—whether through error, privilege misuse, or social engineering.
Why is this? Because humans don’t think like machines. We don’t process threats with perfect logic or total attention. Instead, we rely on mental shortcuts—known as cognitive biases—and intuitive, fast thinking. These are the exact mechanisms attackers manipulate. They exploit these psychological patterns with deliberate tricks and tactics designed to influence behavior and decision-making.
And they’re getting very good at it.
The CEO Scam: A Masterclass in Behavioral Exploitation
Let’s take one of the most chilling and common examples: the CEO fraud, also known as Business Email Compromise (BEC). Imagine this scenario:
An accounts payable manager receives an urgent email from the CEO. The boss is traveling, their phone is off, and they need a confidential wire transfer completed immediately to close a sensitive deal. The email is convincing: correct domain, similar tone, even a realistic signature block. The pressure is on.
The employee complies.
Except it wasn’t the CEO. It was a hacker who spoofed the address and crafted the message using publicly available information. No malware. No brute-force attack. Just behavioral precision.
This exploit works because it leverages two powerful cognitive factors:
- Authority bias – We tend to comply with directives from perceived leaders.
- System 1 thinking – Under pressure, we default to fast, intuitive decisions, not slow, analytical reasoning.
System 1 and System 2 thinking—concepts from Daniel Kahneman’s Thinking, Fast and Slow—are central here. System 1 is automatic and emotional; System 2 is deliberate and logical. Social engineering attacks are engineered to short-circuit System 2 and exploit System 1.
These patterns aren’t new, but understanding them in the context of cybersecurity is. And that’s why our webinar series exists: to bring together the behavioral economists, white hat hackers, policy leaders, and human factors experts who rarely occupy the same (virtual) room.
Behavioral Engineering: The Response to Social Engineering
What’s the takeaway? Your employees aren’t security liabilities, they’re security infrastructure. But just like firewalls or VPNs, they need to be designed and configured properly.
That’s where behavioral engineering comes in.
Rather than treat behavior as a side effect, forward-looking companies treat it as a design space. They ask: how do we make the secure action the easy action? How do we structure decisions, defaults, feedback, and even consequences to steer people toward better choices?
This isn’t about more training. Most phishing awareness campaigns fail because they rely on System 2 (rational thought) in moments that demand System 1 (rapid judgment). Instead, organizations need behavioral defaults; things like flagging external emails, time delays for large transfers, or AI prompts that suggest alternative actions.
That leads to the next big question: how do these defaults become part of security standards that guide people to better behaviors? Enter security policy, real time interventions, and gamification.
Policy Evolution: Moving to Behavior-Centric Governance
Evolving from static, one-size-fits-all policies to behavior-centric governance means treating secure actions as intentional outcomes, not assumptions. This requires defining and governing specific, observable behaviors as part of your policy set while explicitly accounting for cognitive vulnerabilities and context. By aligning policy with how people actually think and act, you can influence decisions at the moment they happen, not just through after-the-fact guidance.
Interventions: Personalized Security Guidance On Demand
The future lies in just-in-time, context-aware guidance that adapts to individual risk and behavior. By layering behavioral signals with real-time data, organizations can deliver tailored interventions (e.g. nudges, prompts, or policy clarifications) at the moment they’re needed.
Think of it like GPS for security: instead of giving someone a manual and wishing them luck, you guide them dynamically along the path. Whether it’s a prompt to slow down a high-risk action, a gentle reminder about data handling practices, or an AI-powered suggestion to reroute a task securely, the goal is the same: empower people to make better decisions, not just prevent bad ones.
This is where behavioral science meets security policy, and where the groundwork for gamification begins
Gamification: Driving Engagement, Not Just Compliance
Gamification takes this a step further by adding motivation to the mix. Security isn’t exactly the most exciting part of someone’s job. But when you layer in game mechanics—progress, feedback, social proof—you transform behavior from compliance to engagement.
Done right, gamification taps into intrinsic drivers like mastery, autonomy, and purpose. It helps reframe security not as a burden, but as a shared game with high stakes and tangible wins. And when it goes beyond simulation into real-world intervention paired with AI, the potential for scalable defense is endless.
Building a Cognitive Security Culture
This shift isn’t just tactical, it’s cultural. Organizations that thrive in this new threat landscape build security mindsets, not just protocols. They understand that the best technical defense still fails if people hold the door open to the attacker, whether that’s literally or metaphorically.
Building a cognitive security culture means:
- Recognizing human behavior as a legitimate attack surface
- Applying behavioral insights proactively in policy and product design
- Using gamification to create continuous engagement, not one-time compliance
- Prioritizing simplicity, clarity, and psychological safety in all communications
From Silos to Strategy: Convening Experts to Guide Security Leadership on this Journey
The CISO of the future must think more like a behavioral designer and less like a sysadmin. Just as product teams obsess over UX flows, security teams must obsess over cognitive friction points and decision architectures.
Your firewall can’t stop a well-timed email that triggers fear, urgency, and trust. But a well-trained mind can.This shift demands collaboration because none of this work happens in a vacuum. If we’re going to meet the moment and truly innovate in cognitive security, we need to stop thinking in silos. That’s why our new webinar series is designed to cross boundaries: bringing together CISOs, researchers, designers, and behavioral experts who don’t normally talk to each other, but must.
Because if attackers are coordinating across disciplines, defenders should be too.
Join us For a Webinar on Cognitive Security
On June 25th we’ll be bringing together some of the best minds in Cognitive Security to talk about what it is, why it matters now more than ever, and how to action it in your organization in the context of behavior and management strategy.
Register now and join Cognitive Security 101: Protection for the Human Attack Surface for free.